WireShark is an awesome packet sniffer tool that is free. It is a complicated tool and in the hands of a pro – probably extremely powerful. Unfortunately it is extremely hard to understand and use.
What I wanted it to do is tell me if packets from my VPN connection tool were at least hitting the network adapter (Probably the simplest thing that you can use WireShark to do – determine if packets destined to a certain address are hitting your network adapter).
Step 1: Install WireShark
Get it from sourceforge at http://sourceforge.net/projects/wireshark/files/ (or www.wireshark.org)
The basic options should be good for everyone.
Step 2: Start up WireShark.
Step 3: Under interface list you should see all your network adapters. Select the one that you are using for trying to connect to the destination address.
In my case, I had 2 interfaces listed – one for the wired port and the other for the wireless port. The wireless port for some reason was named Microsoft on my computer. This is the one I selected.
Selecting the interface will open a new window: The Wireshark Capturing window.
Step 4: The wireshark capture window.
If you selected the correct interface you should immediately begin seeing a whole bunch of traffic, representing all the current connections that your computer is making through this interface. (If you dont see any traffic, open up your browser and try and browse to some site. This should begin listing traffic in the window. If not, you most probably picked the wrong interface).
Step 5: Test if you are able to communicate with the destination.
What you need for this is the IP address of the destination (at least thats how I was going to do it).
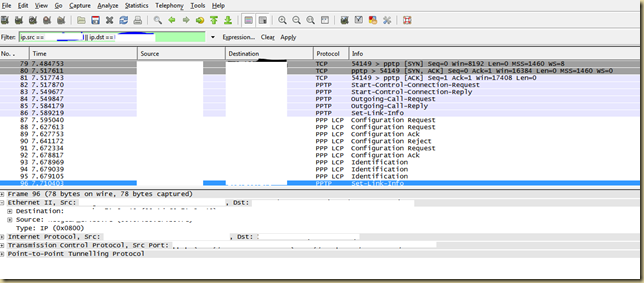
In the capture window there is an filter text box. Type the following expression “ip.src == xxx.xxx.xxx.xxx || ip.dst == xxx.xxx.xxx.xxx”, where xxx.xxx.xxx.xxx is the IP address of the destination that you are trying to connect to. The expression will display only those packets that either originated at the other IP address or are destined to that IP address. This will make it easier to figure out if the connections are going out correctly.
Now try and run the operation that will initiate the external connection. If you see activity in the window, then things are working and the problem is elsewhere. If you dont see activity, then the issue is probably on your end – and the first place to look would be your firewall rules.
The activity will look something like the following window:
Note: There are only 2 things to learn from this post: Use WireShark when you need to look at network packets at a low-level and the expression ip.src == “xxx.xxx.xxx.xxx” || ip.dst == “xxx.xxx.xxx.xxx”. Everything else is just extra information!

No comments:
Post a Comment