Have you ever got the "This implementation is not part of the Windows Platform FIPS validated cryptographic algorithms." exception while trying to use some of the classes in the "System.Security.Cryptography" namespace?
The exception normally thrown is a "TargetInvocationException" exception and the message that accompanies it is usually the unhelpful "Exception has been thrown by the target of an invocation". It is only when you drill down into the InnerException that you see the "This implementation is not part of the Windows Platform FIPS validated cryptographic algorithms." message. The reason that this exception is thrown is that you have tried to use a cryptographic algorithm that is not FIPS compliant.
What is FIPS compliance? FIPS stands for Federal Information Processing Standards. (link to more information) and are US Government standards that provide a benchmark for implementing cryptographic software.
WindowsXP and later operating systems have both FIPS compliant and non-compliant algorithms that can be used by developers. FIPS compliant algorithms are those that have been validated by the FIPS 140 program. One can call both the compliant and non-compliant algorithms as the check for FIPS compliance is by default turned off.
How do you turn on and off FIPS compliance checking:
Two methods:
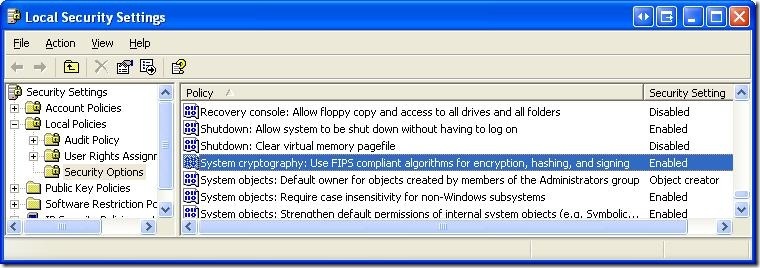
1. Go to Control Panel -> Administrative Tools -> Local Security Policy
Enable the setting for "System cryptography: Use FIPS compliant algorithms for encryption, hashing, and signing"
2. Another method is to directly edit the registry by setting the following value to 0 (disable) or 1 (enable)
HKLM\System\CurrentControlSet\Control\Lsa\FIPSAlgorithmPolicy
Alternatively you can copy the following lines into a registry script file (.reg) and run it.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa]
"fipsalgorithmpolicy"=dword:00000001
Note: One thing that I am not certain off is that this option might be available only on Windows XP Professional OSs and not in the basic Windows XP OS. I havent been able to confirm this via documentation - but the option is not available on my home machine (Windows XP), but is available on my work machine (Windows XP Pro).
For Developers:
So what does this mean for developers? If you ever envision your software running on a government computer (especially in the US), you should turn on FIPS compliance checking. This way, your application that uses cryptography algorithms provided by the OS will work on all machines and you wont have to deal with the "Exception has been thrown by the target of an invocation".
For .NET Developers:
FIPS compliance checking (if turned on in the local security policy) I think was introduced starting in version 2.0 of .NET. Unfortunately, the MSDN documentation on FIPS compliance is pretty skimpy and there is no list of the algorithms in the "System.Security.Cryptography" namespace that are FIPS compliant. (Also there is no property that can be checked or an interface or base class that FIPS compliant algorithms implement - which would allow for runtime checking - hint, hint MS).
So here is a quick list that I obtained by using reflection (C# code is below)
FIPS compliant Algorithms:
Hash algorithms
HMACSHA1
MACTripleDES
SHA1CryptoServiceProvider
Symmetric algorithms (use the same key for encryption and decryption)
DESCryptoServiceProvider
TripleDESCryptoServiceProvider
Asymmetric algorithms (use a public key for encryption and a private key for decryption)
DSACryptoServiceProvider
RSACryptoServiceProvider
Algorithms that are not FIPS compliant
HMACMD5
HMACRIPEMD160
HMACSHA256
HMACSHA384
HMACSHA512
MD5CryptoServiceProvider
RC2CryptoServiceProvider
RijndaelManaged
RIPEMD160Managed
SHA1Managed
Useful Links:
- The effects of enabling the "System cryptography: Use FIPS compliant algorithms for encryption, hashing, and signing" security setting in Windows XP and later versions (link)
- FIPS 140 evaluation (link)
- Enforcing FIPS Certified Cryptography (link)
- .NET 2.0 and FIPS (link)
Code:
Here is some quick C# code to help you test for FIPS compliance:
Remember to enable FIPS compliance using one of the methods suggested above before running this code, otherwise all the algorithms will come up as being FIPS compliant.

11 comments:
Our small government development shop is using VS 2005. When the AD pushed down a GPO that enforced the fipsalgorithmpolicy = 1, we could no longer debug. I ran across at least 10 references/links to either change the reg value (nope, see GPO) or mod the application's web.config <web> section to include the <machineKey> mod which didn't work.
What DID work for us was editing the devenv.exe.config.
<configuration>
<runtime>
<enforceFIPSPolicy enabled=”0” />
</runtime>
</configuration>
See link here which discusses how to fix it if using VS 2008.
Thank you thank you thank you.
I'm using Windows 7 and VS.Net 2008 and up until 2 days ago everything was working fine. I updated some of my 3rd party tools and BANG - "This implementation is not part of the Windows Platform FIPS validated cryptographic algorithms". Thanks to your post I could turn off FIPS compliance checking.
Thanks again.
Neville - Cape Town - South Africa
I'm using Visual Studio 2008 SP, and Framework 3.5 SP1 WCF Tools ona Windows 7 to connect to an HTTPS web service and I get this exception.
I've tried to enable the local security policy mentioned above, but it doesnt' work (I've restarted the machine too).
In other machines with the same configuration (as I can see) works fine!
Have you any idea? I've googled it and I haven't found anything...
Thank you!! This was very helpful...
Thankyou!!! This was very helpful...
Thanks a lot..
Hi ,
I see SHA-512 is FIPS complaint.
http://csrc.nist.gov/publications/fips/fips180-2/fips180-2.pdf
I even tried,
SHA512CryptoServiceProvider
http://msdn.microsoft.com/en-us/library/system.security.cryptography.sha512managed(v=vs.90).aspx#1
But, When the FIPS mode is turned on, It throws exception.
Is there a diferrent implementation of SHA-512 which is FIPS complaint?
Thank you,
Isaac
AesCryptoServiceProvider works fine as a FIPs compliant symmetric algorithm too. In fact I had a problem with TripleDES, with an error regarding 'known weak key', so changed to just DES, but then read that was only for legacy systems, so tried Aes, and everything worked great.
@Isaacdudes - (for posterity here) perhaps you are using a build with debugging enabled or are debugging in the IDE? Debugging enabled throw exceptions even when using compliant crypto providers, such as the SHA512CryptoServiceProvider.
You can turn this behaviour off locally to allow debugging. Discussion can be found here:
http://forums.asp.net/t/1265047.aspx
Thanks. This was very useful.
Is HMACSHA512 FIPS complaint? When i run the below code it's not throwing any error even after turn on of registry flag HKLM\System\CurrentControlSet\Control\Lsa\FIPSAlgorithmPolicy
I'm using dot net framework 4.5
byte[] bR = null;
byte[] data = Encoding.UTF8.GetBytes("Hello, world!");
byte[] data1= Encoding.UTF8.GetBytes("Test Hello, world!");
using (HMACSHA512 Mac2 = new HMACSHA512(data))
{
Mac2.Initialize();
bR = Mac2.ComputeHash(data1);
}
Please let us know your comments on the same
Post a Comment